Watch our recorded webinar:
Solving the Challenge of Secure Privileged Remote Access to your OT Environment

All done simply without VPN with the highest granularity of security controls incl. full audit & forensics
Granting remote access to 3rd party vendors and external consultants to your manufacturing network is a bit like walking a tight-rope: it is a demanding balancing act that requires ultimate control (cybersecurity), while still providing freedom of movement (productivity) .. and if you fail, the stakes can be very high.
SecuriOT help solve the challenge of securely bringing support & service engineers into your OT infrastructure via privileged remote access.
Privileged remote access will take your OT-security to the next level, and can seamlessly integrate with your existing security platforms.
See our webinar on privileged remote access and hear how SecuriOT and BeyondTrust can enable secure access to your manufacturing floor and production IT.
We will also show you, how to securely provide remote access for “classic” OT use cases:
- A technician needs to make changes on a SCADA server (e.g. GE iFix)
- A technician needs access to a specific PLC to make changes (e.g via Step7 or Machine Edition)
- A Service Provider does maintenance tasks in OT specific applications (such as back-up & versioning software VersionDog from Auvesy)
In addition, you will hear how to find inspiration and guidance from standards such as IEC62443 or the NIST framework to enable you to tie technologies into the daily work around cyber security.
Agenda:
- Welcome
- SecuriOT presentation
- OT remote access
- Problem scope
- Standards & compliance, policies & procedures
- OT remote access
- BeyondTrust presentation
- PRA
- Product introduction, functionality & architecture
- Highlighted functionality particularly suited to OT environments
- Live demos
- Generic functionality
- OT use case examples
- Auditing and reporting
- PRA
Fill out the form below, and get a link to the video – How you solve YOUR remote access challenges for OT.

BeyondTrust is the industry leader in universal privilege management. In this recorded session we have included a presentation and demo of BeyondTrust Privileged Remote Access.
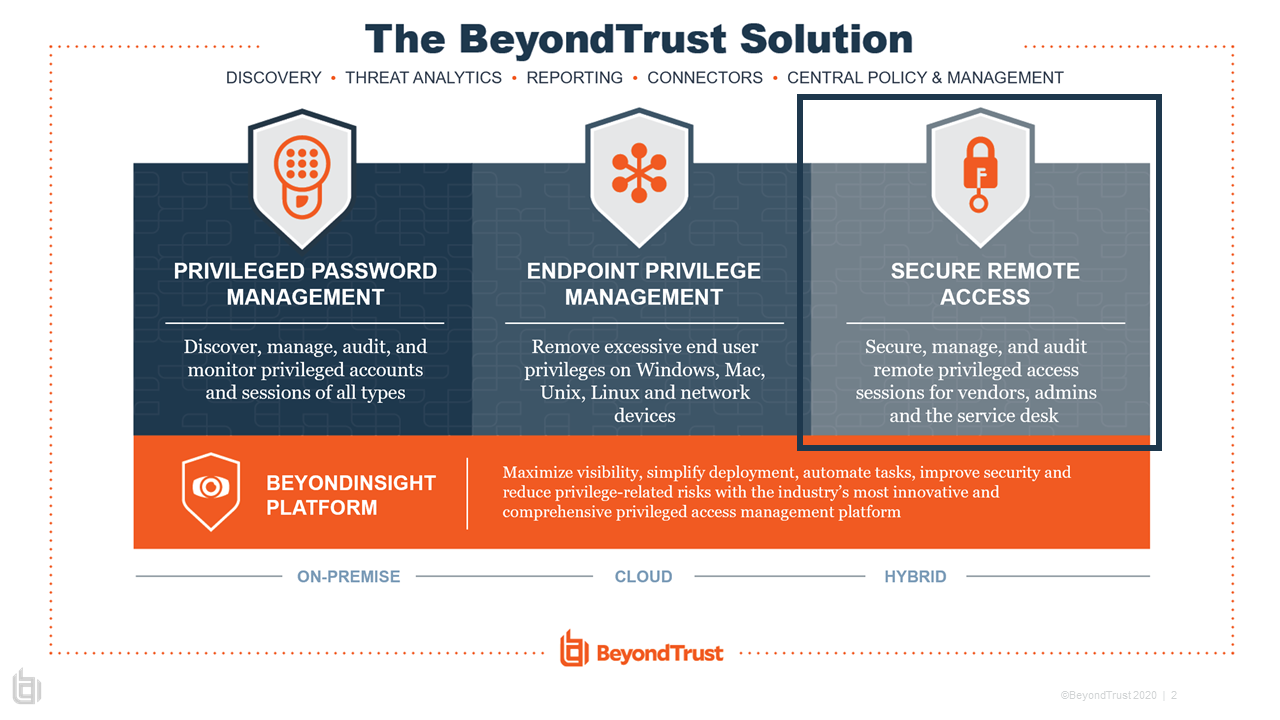
Control, manage and audit vendor & internal remote privileged access
BeyondTrust Privileged Remote Access provides visibility and control over third-party vendor access, as well as internal remote access, enabling organizations to extend access to important assets, but without compromising security.
Business Benefits
Control
Enable granular access to specific systems, improving security and eliminating “all or nothing” access to vendors or internal resources.
Audit, Compliance & Forensics
Centrally secure and audit vendor access across a variety of environments and meet compliance & forensics mandates.
Manage
Eliminate unnecessary privileges – without impacting the user’s ability to perform their role.